Home>Configuration
Contents
- 1 Configure Base RavenNuke™
- 2 Configure NukeSentinel™
- 3 Additional Add-Ons
- 3.1 nukeWYSIWYG™ featuring FCKeditor 2.6.4 and the kses filter class
- 3.2 nukeFEED™ (Version 1.1.1)
- 3.3 nukePIE™ featuring SimplePie and BoxOver
- 3.4 HTML Newsletter (Version 1.4.0)
- 3.5 TegoNuke™ ShortLinks (Version 1.3.1)
- 3.6 TegoNuke™ Dynamic Titles (Version 1.2.0)
- 3.7 TegoNuke™ Mailer (Version 1.1)
- 3.8 GCalendar (Version 1.7.0)
- 3.9 Forum Attachment Mod
- 3.10 Content Plus (Version 2.2.1) from slaytanic.sourceforge.net
- 3.11 Shout Box (Version 8.5.2) from ourscripts.net
- 3.12 Error Documents
Configure Base RavenNuke™
Most settings have already been pre-configured in the installation process so far. There are just a few more settings that you may want to configure at this time. It is suggested that you open up another browser session and point your address bar to http://YOURDOMAIN.com/admin.php (your path may be slightly different). Here are some suggestions on what settings you may wish to review and adjust within the Admin Control Panel (ACP):
- ACP -> Preferences
- Default language, default theme, support for multiple languages, and news submission information.
- ACP -> Forums -> Configuration
- System timezone and cookie settings (some recommend setting the cookie domain to your own, but in most cases the default will work fine).
These settings can always be adjusted later but having them correct at the outset will help to prevent initial problems. When done configuring the core nuke settings of your choosing, return to the next step in this HowToInstall manual.
Once configuration is complete you should either remove the INSTALLATION folder (preferred) or at the least RENAME it (to something no-one can guess). You will not be able to access your site until you do, and, even more importantly, someone could use the installSQL.php to completely wipe out your RavenNuke(tm) site!
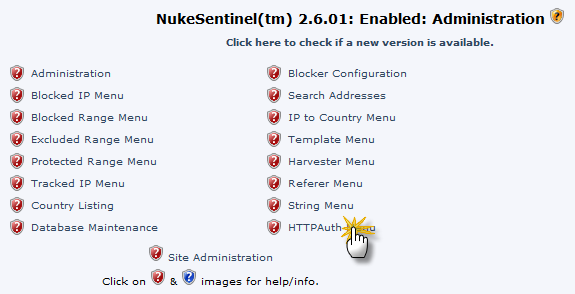
Configure NukeSentinel™
If on a *nix host, use your FTP client or control panel tools to change the permissions on the .htaccess, .staccess, and ultramode.txt files to 777. These permissions are required now in order to complete the installation and setup; once the installation and setup are complete, we will change these back to something more secure.
Make sure that you have completed the previous steps completely before moving on to configuring NukeSentinel™. NukeSentinel™ has been pre-configured to:
- Track all IP's (for the last 7 days).
- Email Admin, Block, and redirect to Default Page upon the following attacks: Admin, Author, CLike, Union, Filters, and Referer.
- Email Admin only for Script attacks, as NukeSentinel™ is very aggressive in keyword matching and there are many false positives, so we leave this up to the Admin to decide.
Click on Blocker Configuration and review the settings for all the blockers. Most have been preset but you should still review them all. If you change any settings, be sure to save them prior to moving onto a different blocker.
Now you are going to get into a part of the instructions where you need to follow exactly and literally. These instructions will allow you to add additional security to protect your admin.php file from being compromised. In other words, there will be an additional sign on screen which provides an extra layer of security for the standard RavenNuke™ Administration Control Panel (ACP). Before you begin these steps, we recommend that you sign onto your host's file manager for instance, through CPANEL or VDECK or whatever other means your host provides to access your files directly. Go to the directory that contains the "root" of RavenNuke™ (i.e., where mainfile is located) and be ready to edit files or change permissions.
Now start setting up security by going to NukeSentinel™ administration from the ACP. Click on Admin Auth List, you should see the NukeSentinel™ ADMIN record that you added during Configuration (setup.php). Make a note of the username and password, they will be needed later.
At this point you should be able to SAFELY activate the Admin Access Protection part of NukeSentinel™. Go back to the NukeSentinel™ Administration main panel. In the Administrative Settings section you should see a drop down box beside Admin Auth:. In many cases, you will see "Off", "Admin HTTPAuth", and "Admin CGIAuth" as options. If "Admin CGIAuth" is NOT listed, simply click "Admin HTTPAuth" and save the settings.
If "Admin HTTPAuth" is not in the list skip over the next two paragraphs.
So, if you are reading this, then you have Admin HTTPAuth and you have selected it. You will now be prompted with the standard browser HTTP Authentication pop up. Type in your NukeSentinel™ id/pass and it should then let you in. If it does, close all browser sessions that you might have open so we can REALLY test this. Open up a new, single browser sessions and type http://www.YOURDOMAIN.com or http://www.YOURDOMAIN.com/html and select GO or press enter. You should see your nuke site with the Welcome message. Next, type http://www.YOURDOMAIN.com/admin.php or http://www.YOURDOMAIN.com/html/admin.php and select GO or press enter. You should be prompted with the HTTP Authorization screen. Enter your NukeSentinel™ id/pass and submit it. Assuming it works, you should now see the regular nuke Admin login screen. Enter your nuke admin id/pass and submit it. You should now see your ACP.
Once the above is working for you, be sure to read the section on Protecting Your Forums Admin Folder at the bottom of this page.
If you are reading this, then you have skipped here because Admin HTTPAuth is not on the list of available Administrative Settings. In this case we are going to need to activate what we call CGI Auth which is equivalent to HTTP Authentication but using .htaccess and .staccess files. To do this:
- Change your permissions on both .htaccess and .staccess to 777.
- Place the paths to .htaccess and .staccess in the NukeSentinel™ Admin Control Panel.
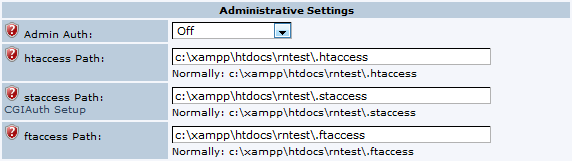
- Select CGI Auth Access from the drop down box.
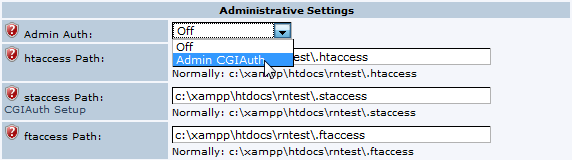
- Save your settings up to this point. We will be coming back here, but first ...

- From the NukeSentinel™ Admin Control Panel, select HTTP Auth menu then Scan For New Admins.
- Now select Admin Auth List and make sure that all admins have been assigned passwords.

- At the top of the list of admins you should see a link that says Build CGIAuth file. Click it. That will build your .staccess id:pass file.

- Now click on the Administration link to bring you back to the main NS ACP. Scroll down to the .staccess box, you will see a link that says CGI Auth Setup. Click it. It should produce a new window with the following information:

Since you already have a window or tab open where you can edit the .htaccess file just save this text into .htaccess. If you neglected to open such a window then open it now and save the text in .htaccess. The text that is generated will look like this:
Note:Some or all of the below .htaccess code may already be present in your .htaccess file. If you see that your .htaccess file already has the code, then you only need to verify that the USERNAME and path to .staccess are correct.
# -------------------------------------------
# Start of NukeSentinel(tm) admin.php Auth
# -------------------------------------------
<Files .staccess>
deny from all
</Files>
<Files admin.php>
<Limit GET POST PUT>
require valid-user
</Limit>
AuthName "Restricted by NukeSentinel(tm)"
AuthType Basic
AuthUserFile /home/USERNAME/public_html/.staccess
</Files>
# -------------------------------------------
# End of NukeSentinel(tm) admin.php Auth
# -------------------------------------------
USERNAME will be your username and the path may be different
- Change your permissions on both .htaccess and .staccess back to 666.
- If you find yourself locked out of your ACP after these steps you can temporarily comment out the lines that you have just added to .htaccess. Just put a # character in front of all the lines you added. This will give you access again while you resolve the problem. You should probably check to see that the appropriate .staccess file has been written. It will be one line with a username and encrypted password in it.
- Some or all of the above .htaccess code may already be present in your .htaccess file. If you see that your .htaccess file already has the code, then you only need to verify that the USERNAME and path to .staccess are correct.
Flood Blocker Settings
To use the Flood Blocker you must first set the permissions of the .ftaccess file to 666 and enter the path to the file in the NukeSentinel™ Admin Control Panel.
The Flood Blocker can then be activated in the Blocker Configuration menu.
Protecting Your Forums Admin Folder
There are numerous attempts from hackers to try and exploit the Forums admin scripts by calling them directly. It is recommended that you also protect the entire modules/Forums/admin folder with a similar approach to admin authentication.
If you are using "CGIAuth", rename the rn.htaccess file that is in modules/Forums/admin to .htaccess and then modify the line for AuthUserFile to match what you have within the .htaccess file that is in the root of your RavenNuke™ installation. This will also protect your Forums admin folder using the same NukeSentinel™ admin auth userid and password!
If you using "HTTPAuth", see the Protecting Your Forums Admin Folder thread in the RavenPHPScripts support forums.
Additional Add-Ons
nukeWYSIWYG™ featuring FCKeditor 2.6.4 and the kses filter class
nukeWYSIWYG™ from http://nukeSEO.com is integrated into this release of RavenNuke™. If you wish to turn this OFF, you may do so by a simple edit to the rnconfig.php script (self-explanatory).
Administrators are authorized to upload files through the editor. Files are installed to different directories, depending on the type. These directories are installed with RavenNuke™. If you wish to allow uploads through the editor, set permissions on these directories to 766 or 777 (for web hosts that are running PHPSuExec or SuExec, you may be able to get away with even 700 - tighter permissions the better - check with your host):
uploads/file
uploads/flash
uploads/image
uploads/media
nukeFEED™ (Version 1.1.1)
nukeFEED™ from http://nukeSEO.com is integrated into this release of RavenNuke™. nukeFEED™ creates outbound feeds using content from this RavenNuke™ site, using modern syndication formats like RSS 2.0 and ATOM. Feeds created by nukeFEED™ are available in LINK tags in the HEAD section of the page, allowing visitors to subscribe to your feeds using their browser or feed reader. Visitors can also preview feeds and subscribe to feeds using popular web-based feed readers.
Two feeds (last 10 news items, and last 10 forums posting) are created by default, either when installing RavenNuke™ or the first time you access the nukeFEED™ administration function. These 2 feeds are used by backend.php and forumsbackend.php, respectively, which display the feeds in RSS 2.0 format.
nukePIE™ featuring SimplePie and BoxOver
nukePIE™ from http://nukeSEO.com is integrated into this release of RavenNuke™ and replaces the block feed reader, which displayed RSS 0.91 formats. nukePIE™ enables RavenNuke™ sites to display feeds using modern syndication formats like RSS 2.0 and ATOM. By default, addition feed item information (including full HTML with images) is displayed in a popup using the BoxOver script. This can be disabled using a setting in the rnconfig.php file (shown below).
/*********************************************************************************
* nukePIE
* http://www.nukeSEO.com
* Copyright ª 2007 by Kevin Guske
**********************************************************************************
* BoxOver with nukePIE:
* true = Display full HTML description of feed item as Boxover tooltip /popup
* false = Display text-only description as title tag on feed link
**********************************************************************************/
$useBoxoverWithnukePIE = true;
As with the nukeWYSIWYG editor above, the /cache directory needs to be made writeable so that SimplePIE can cache the XML content.
HTML Newsletter (Version 1.4.0)
Rob Herder (montego) took over the development and support for this module after version 1.0 and made significant enhancements along the way. This module allows one to create and send out HTML formatted mailings using a simple template system to where you can create your own "look and feel". For a more detailed explanation of features (many), please read the README.txt file that is in the AddOnFiles\HTML_Newsletter\ directory within this Distro.
Make sure and set the permissions on the modules/HTML_Newsletter/archives directory as 777, otherwise, the module will be unable to write the newsletters to the file system (for web hosts that are running PHPSuExec or SuExec, you may be able to get away with even 700 - tighter permissions the better - check with your host).
TegoNuke™ ShortLinks (Version 1.3.1)
After the original author took down the GT-NextGEn site and apparently stopped developing and supporting the great "GoogleTap" / "GTNG" concept (i.e., shortened URLs), Rob Herder (montego) decided to continue with development and has released this under his TegoNuke™ brand and is calling it "ShortLinks". For a more detailed explanation of what this is used for, please read the RavenNuke_README.txt file that is in the AddOnFiles\TegoNuke\ShortLinks directory within this Distro.
This feature comes defaulted as OFF and it can be turned ON at any time (with a rnconfig.php setting AND .htaccess edits); however, a word of caution, once your URLs are crawled by a search engine, you will not want to turn this off!
TegoNuke™ Dynamic Titles (Version 1.2.0)
This feature may be used to modify the PHP-Nuke generated page titles to be more descriptive based on the module at the time. For some modules, such as Forums, it even generates different titles based on the Forum, Topic and/or Post that is being viewed / crawled. This greatly helps with search engine indexing and ranking. This feature comes defaulted to OFF, but may simply be turned ON in the rnconfig.php script (self-explanatory).
NOTE: Dynamic Titles originally came from the last known update from sixonetonoffun and was cleaned up a little bit by Montego and Raven, and now further enhanced and supported by Montego.
TegoNuke™ Mailer (Version 1.1)
This feature may be used for those hosting environments where the PHP mail() function has been disabled by the host (for security reasons). Simply access the TegoNuke™ Mailer in the Administration Control Panel and follow the directions within the pop-up help. Most likely your host will require authenticated SMTP. Make sure you have all your SMTP access settings available as you will need these to configure the mailer. Check with your host as to the proper settings if you are unsure. We have also found it useful (if you are allowed multiple email accounts with your hosting plan) to set up a separate email account with the different password than your host account (actually, we highly recommend it) and use that account as your mailer.
NOTE: if you can set up your mail client (such as Thunderbird or Outlook) to access your hosted email account to both send and receive, then those will be the same settings that you will need to set up the Mailer.
GCalendar (Version 1.7.0)
GCalendar is an event calendar module for PHP-Nuke Content Management Systems, with special integrated support for RavenNuke™. GCalendar features: monthly, weekly & daily views; repeating events; international date and time format support; user submitted events with optional admin approval; use of CSS so admins can easily customize the appearance of the application without changing code; RSVP feature; email event to friend feature; integration with RavenNuke™'s nukeWYSIWG editor; support for NSN groups; calendar blocks; and more.
For GCalendar support, please visit the GCalendar Sourceforge.net support page.
Forum Attachment Mod
This mod allows one to enable the uploading of files of various types within the Forums.
Make sure and set the permissions on the modules/Forums/files directory as 777, otherwise, the module will be unable to write the uploaded files to disk (for web hosts that are running PHPSuExec or SuExec, you may be able to get away with even 700 - tighter permissions the better - check with your host).
Content Plus (Version 2.2.1) from slaytanic.sourceforge.net
Content Plus is a revamped distribution of the default PHP-Nuke/RavenNuke content module. Based upon the original module developed by former PHP-Nuke developer Francisco Burzi as well as the Chatserv Content Hack but heavily improving functionality, usability and appearance. We have not yet integrated this into the core system (it will be integrated in the next RavenNuke™ release), so you are left with installing this yourself, but just follow the instructions found in AddOnFiles/Content_Plus/README. Some of the great features:
- Greater, faster, stronger, cuter
- 100% XHTML 1.0 compliant
- Users can submit content pages
- You can set/upload a custom image for categories
- You can set a featured content for each category
- You can easily print and/or export pages to PDF format
- You can share content pages with friends
- Automagic integration with PhpNukeMailer/TegoNuke Mailer
Shout Box (Version 8.5.2) from ourscripts.net
This shout box has been "tweaked" by Gremmie for RavenNuke™ in order for it to run under XHTML 1.0 Transitional compliance. It has been a very popular requested script and we felt that since it required tweaking in order to run under RavenNuke™, why not at least provide it in the download package. We have not integrated this into the core system, so you are left with installing this yourself, but just follow the instructions found in AddOnFiles/Shout_Box/install.txt.
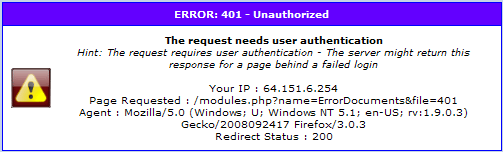
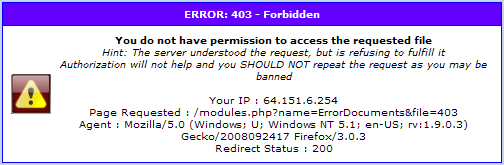
Error Documents
This module replaces your servers standard error documents. To use this module, it must be activated in the modules admin, After you have activated the error module, please be sure to test it by testing an erroneous url on your site and making sure the appropriate error message appears. If there are any problems, you will often get an indication of what file is missing or incorrectly linked from your server’s error log. The most common problem is with some default lines at the bottom of the distribution’s htaccess file (in the root directory (the same one with mainfile)). These lines read:
ErrorDocument 400 /modules.php?name=ErrorDocuments
ErrorDocument 401 /modules.php?name=ErrorDocuments ... etc. for each type of error
As the documentation in the htaccess file states, you may need to adjust these for where you have placed your RN distribution in the directory structure. Most commonly your document root is /public_html and you have placed RN in a html directory within that. If that is the case, you would need to adjust the htaccess lines to read:
ErrorDocument 400 /html/modules.php?name=ErrorDocuments ... etc.
The module is also multilingual and the defines can be changed within the language directory of the module.
Below are a few typical examples of the error messages produced: